Researchers at the University of California have identified a previously undocumented class of attack targeting the AI agents infrastructure layer, finding that malicious third-party LLM API routers can intercept agent communications, inject code into tool calls, and drain crypto wallets – including, in at least one documented case, executing an actual ETH transfer out of a researcher’s live wallet.
The findings, published in an April 2026 arXiv paper and described by the team as the first systematic analysis of malicious intermediary attacks on the LLM supply chain, elevate what had previously been a theoretical concern into a demonstrated, measurable threat.
What makes this finding structurally significant is the attack surface it exposes – not smart contracts, not private key management failures in the conventional sense, but the routing layer that sits between an AI agent and the underlying language model it queries.
As autonomous AI agents are increasingly integrated into crypto wallets, DeFi protocols, and automated trading workflows, that intermediary layer has become load-bearing infrastructure, and it is currently operating without meaningful security standardization.
DISCOVER: Best crypto to buy right now – CoinSpeaker’s updated guide
How Malicious AI Agent Routers Work: The Intermediary Attack Chain and What It Can Execute Against Crypto Wallets
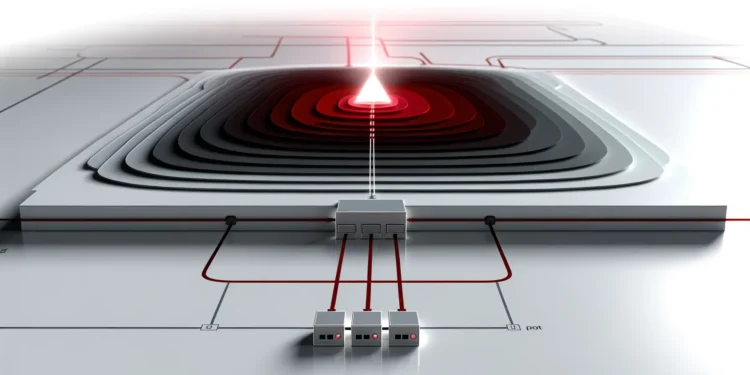
An AI API router, in standard usage, functions as a middleware layer – it receives requests from an AI agent or application, forwards them to one or more LLM providers, and returns responses.
Developers and teams frequently use third-party routers to manage API keys, load-balance across providers, or reduce costs by accessing cheaper model endpoints. The router sits, by design, in a position of full visibility over every prompt, tool call, and response that passes through it.
A malicious router exploits exactly that position. Rather than transparently forwarding agent traffic, it can inspect, modify, or respond to tool crypto calls – the structured commands an AI agent issues to interact with external systems, including wallets.
Source: Arxiv
In the UC researchers’ framework, this enables at minimum three active attack types: injecting malicious code into an AI agent tool execution pipeline, harvesting API credentials and private keys transmitted or referenced in agent sessions, and deploying adaptive evasion logic that delays malicious behavior – waiting, in some documented cases, 50 or more call cycles before activating – to defeat naive monitoring.
The researchers also identified a fourth vector they describe as particularly dangerous in agentic contexts: exploiting “YOLO mode,” the autonomous execution capability present in several major agent frameworks, where the agent acts on tool call responses without human confirmation.
A router that can inject into that loop can, in principle, authorize transactions the user never explicitly approved. That capability is not theoretical – the team confirmed 1 router among those tested actively drained ETH from a researcher’s wallet.
UC Researchers’ Specific Findings: Scale, Confirmed Malicious Behavior, and the Epistemic Limits of an arXiv Preprint
The research team tested 428 routers in total: 28 sourced from paid listings on Taobao, Xianyu, and Shopify storefronts, and 400 obtained free from public community channels. Of those, 9 routers – 1 paid, 8 free – were confirmed to be actively injecting malicious code into tool calls.
Separately, 17 accessed AWS canary credentials the team had embedded as detection tripwires, and 2 deployed adaptive evasion techniques specifically designed to defeat behavioral monitoring. More than 20% of the full sample exhibited malicious behavior or material risk indicators, according to the researchers’ own classification.
The credential exposure data from the team’s poisoning experiments is, if accurate, the most consequential finding in the paper. A leaked OpenAI key placed on Chinese forums, WeChat, and Telegram was used to process 100 million GPT-5.4 tokens and more than 7 autonomous Codex sessions before detection. A weaker decoy credential triggered 2.1 billion billable tokens across 440 Codex sessions and 401 YOLO mode autonomous sessions, exposing 99 credentials in total.
26 LLM routers are secretly injecting malicious tool calls and stealing creds. One drained our client $500k wallet.
We also managed to poison routers to forward traffic to us. Within several hours, we can directly take over ~400 hosts.
Check our paper: https://t.co/zyWz25CDpl pic.twitter.com/PlhmOYz2ec
— Chaofan Shou (@Fried_rice) April 10, 2026
Solayer founder Fried_rice characterized the findings on social media on April 10, 2026, as evidence of “systemic security vulnerabilities” in third-party API routers – a description that aligns with the paper’s own threat model framing.
It is necessary to flag the epistemic status of these claims directly: the paper has not, at time of writing, completed formal peer review through an academic venue. It is an arXiv preprint, and the specific figures – token counts, router behavior classifications, credential exposure tallies – have not been independently verified by a third party.
We suspect the core findings are directionally sound, given the methodology’s apparent rigor and the corroborating detail across multiple reported attack types, but extrapolations beyond the 428-router sample should be treated with proportionate caution.
EXPLORE: Best meme coins to watch – CoinSpeaker’s updated rankings
Disclaimer: Coinspeaker is committed to providing unbiased and transparent reporting. This article aims to deliver accurate and timely information but should not be taken as financial or investment advice. Since market conditions can change rapidly, we encourage you to verify information on your own and consult with a professional before making any decisions based on this content.

Daniel Frances is a technical writer and Web3 educator specializing in macroeconomics and DeFi mechanics. A crypto native since 2017, Daniel leverages his background in on-chain analytics to author evidence-based reports and deep-dive guides. He holds certifications from The Blockchain Council, and is dedicated to providing “information gain” that cuts through market hype to find real-world blockchain utility.