North Korea (DPRK) state-affiliated hackers and threat actors were responsible for more than $2 billion in crypto losses in 2025, a 51% year-over-year increase, despite fewer attacks carried out by the group, according to cybersecurity company CrowdStrike.
DPRK hackers represent the “largest” threat group targeting cryptocurrency users, as measured by the dollar amount of assets stolen, according to the company’s 2026 Financial Services Threat Landscape report. Crowdstrike added:
“Stolen proceeds are almost certainly laundered to fund the regime’s military programs. Compared to 2024, DPRK-nexus adversaries conducted fewer campaigns but achieved significantly higher returns by prioritizing high-value targets.”
The DPRK hackers and scammers focused on targeting Web3 projects and cryptocurrency exchanges because the stolen funds could be “cashed out” and transferred with a greater degree of anonymity than in the traditional financial system, CrowdStrike said.
The countries most targeted by DPRK hackers. Source: CrowdStrike
The report highlights the growing threat of state-affiliated hacking groups targeting cryptocurrency users and industry companies through cybersecurity threats and social engineering scams designed to steal funds and sensitive information.
Related: US sentences ‘laptop farmers’ tied to North Korean IT worker scheme
North Korean hackers infiltrate crypto projects online and offline
In April, the Ethereum Foundation, the organization that oversees development of the Ethereum ecosystem, identified 100 DPRK-backed hackers and threat actors who infiltrated crypto projects.
Typically, these threat actors are remote hires; however, in April 2025, the Drift Protocol decentralized crypto exchange was infiltrated and compromised by DPRK-affiliated technology workers, who met with the Drift Protocol development team.
The Drift Protocol team said that they met the threat actors during a “major” cryptocurrency industry conference and built a working relationship with them over six months.
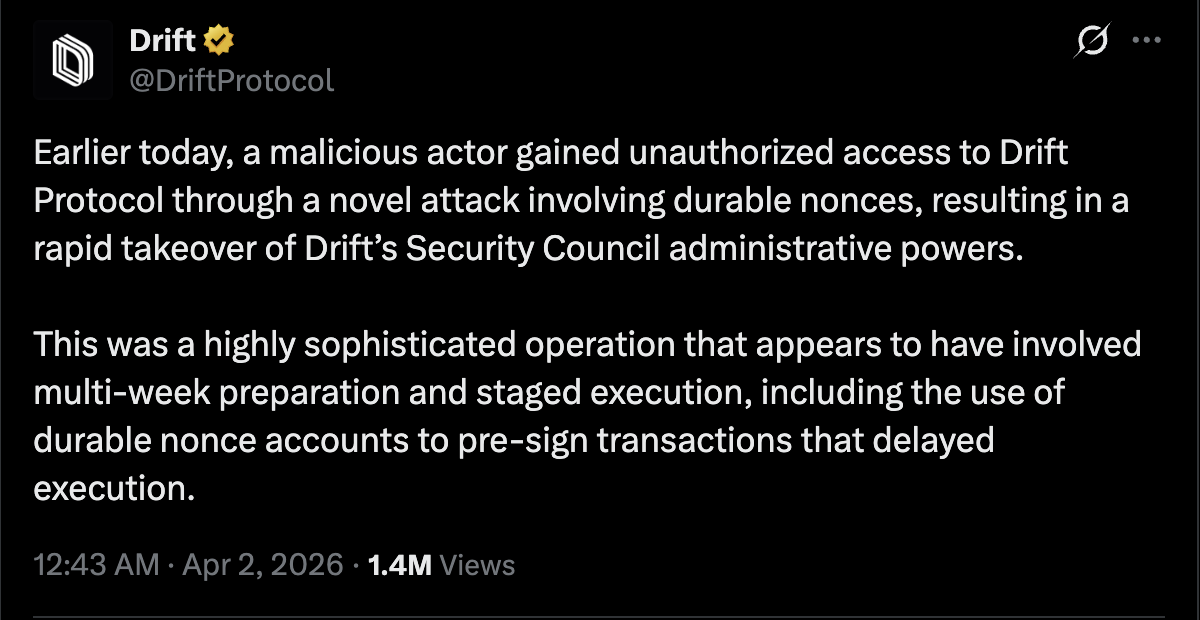
Source: Drift Protocol
During the collaboration, the hackers deployed malware, which compromised Drift Protocol developer machines and caused $280 million in losses.
“It is important to note that the individuals who appeared in person were not North Korean nationals,” the Drift team said, adding, “DPRK threat actors operating at this level are known to deploy third-party intermediaries to conduct face-to-face relationship-building.”
During that same month, Onchain sleuth ZachXBT also documented a group of North Korean information technology (IT) workers who were making $1 million per month working at technology companies.
Magazine: North Korea denies crypto hacks, Upbit’s bank tests Ripple: Asia Express